Two new features related to groups I do really like and think I will use a lot.
Find Groups
Starting with the simplest - the ability to see what groups a person is in by selecting “Find Groups” from their person document. Yes we have had some of this before in the form of the “Manage Groups” dialog in the People and Groups view but this is more detailed, and most importantly printed on screen.
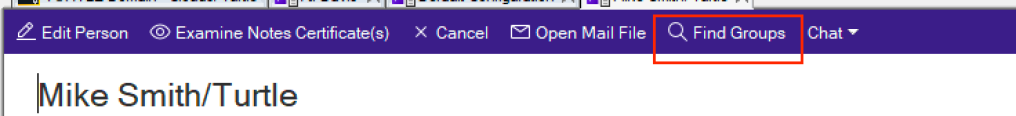
Open any person document and click “Find Groups”
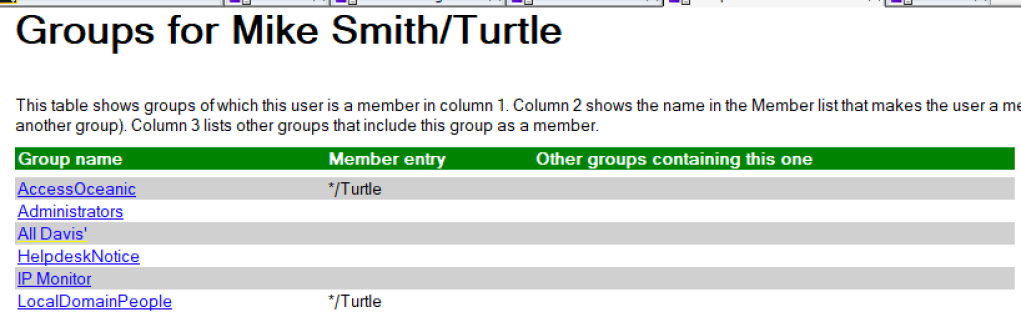
The system will think for a moment then open up a new page with all of that user’s groups listed in it. The group names in the first column are clickable and will open the group document. The 2nd column shows what entry in the group grants that person access if it’s not their explicit name and the third column will show any nested groups that put them in the named group.
AutoPopulating Groups
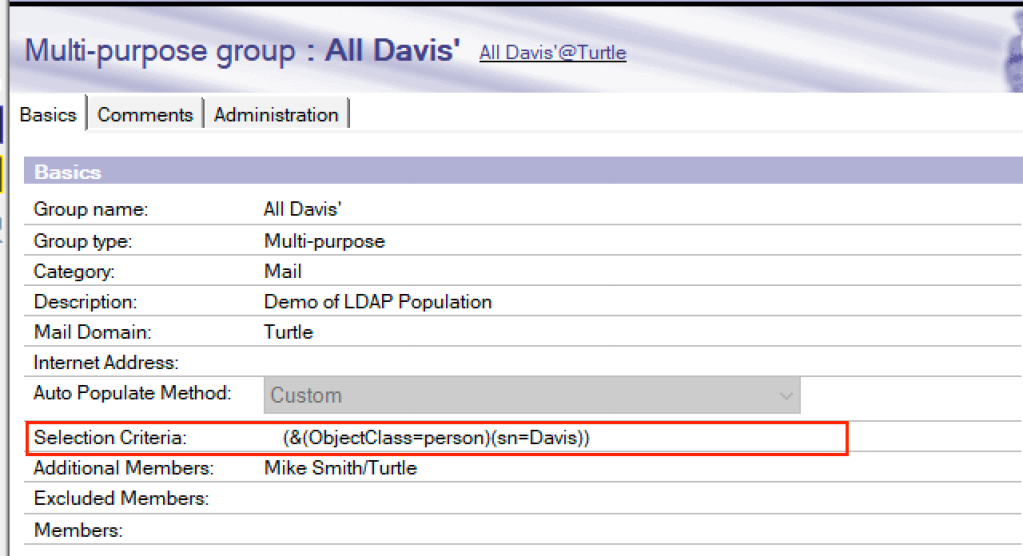
I am betting the new custom autopopulate group feature is going to be heavily used. Certainly by me. We have had the ability to auto populate groups for a while but only by user’s home server never by anything else. Now in v12 we can have groups autopopulate according to any LDAP search we want. For example let’s say I wanted a group that kept itself updated with the names of all people in the Domino Directory having the last name “Davis” (just for giggles). So here I’ve created a group, set it to “Custom” auto populate and written an LDAP syntax that searches for any documents flagged as “person” that also have the last name of “Davis”. We are also able to add other members to the group who otherwise wouldn’t be in there such as Mike Smith and even exclude members.
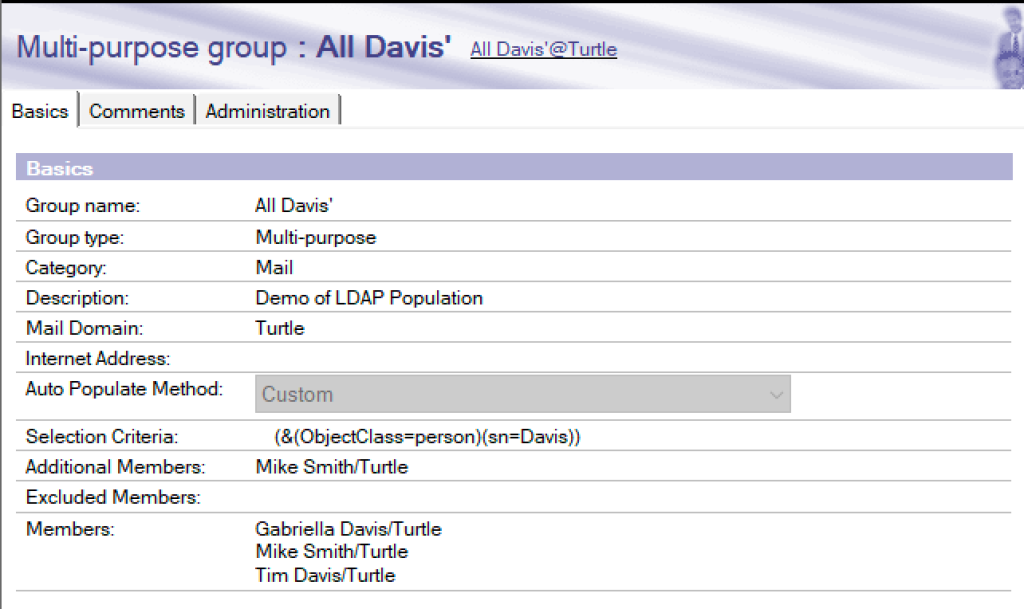
After saving and closing the documents , I checked a few minutes later and my group now shows this, as you can see it has put two Davis’ in the group and added Mike Smith as an additional member. That group membership will continue to be maintained.
You do not need to be running the LDAP task on your server for this to work.
Now think about how useful that is. Groups of people all sharing an internet domain (&(ObjectClass=person)(mail=*.turtleweb.com)) or all at a particular location (&(ObjectClass=person)(Site)). This can be used for any kind of groups including security so if you want to restrict people’s access to an application by their department for instance you can build an autopopulating group that does that.
What if you don’t know how to construct LDAP search syntax? Well it’s not very hard you just need to know some basic rules. When I save the group document it will do a simple LDAP syntax check to make sure your brackets and ampersands look right but you might want to build your search criteria using an LDAP browser yourself first to make sure it’s giving you what you need. I’m a big fan of Softerra’s LDAP Browser which is both brilliant to use and entirely free https://www.ldapadministrator.com/softerra-ldap-browser.htm.
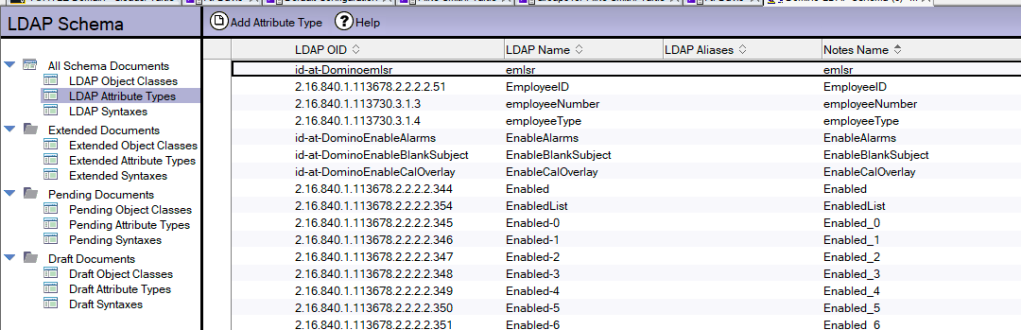
To help you build your syntax it’s good to understand how Domino fields map to LDAP attributes and that is defined in the schema.nsf on your Domino server. The schema.nsf is created or pulled by a server the first time LDAP is run as a task so if your server does not have a schema.nsf just “load ldap” then “tell ldap quit” a few minutes later and one will appear.
For the most part we never touch the schema.nsf but here is an example of its contents that would allow you to see the mappings between fields and attributes.
Would be nice if you could specify an arbitrary LDAP server for that query.